Are multiple tools complicating your security posture?
Prevention, identification mitigation, and management are the key tactics for an effective and secure IT data center. IT departments face the challenge of monitoring operations across an increasingly complex mix of on-premises and cloud infrastructure. Each of these different environments provides tools to enable security, governance, and policy controls for the workloads specific to that environment.
A key challenge for IT is identifying the data that is germane to the problem you are solving. For example, which servers require patching, port management or new subscriptions added without IT awareness.
This complexity usually results in inconsistency across the entirety of your on-premises and extended data center operations. The “multiple management tools scenario” directly impacts the time IT staff spends to ensure internal and external stakeholders have secure access to those systems.
Security Center identifies those systems and provides remediation suggestions and automation capabilities enabling IT to achieve operational efficiency across the hybrid data center.
Azure has expanded its policy and threat detection services to enable IT administrators, security and operations teams to leverage Azure Security Center and Azure Defender across its hybrid data center environments. This blog will provide an overview of each product, how they work in combination, to provide IT staff with a single management pane to ensure compliance and employ threat detection tools across the IT domain.
Azure Security Center’s features cover the two broad pillars of cloud security:
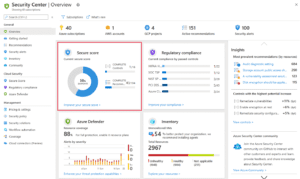
- Cloud security posture management (CSPM)– Security Center is available for free to all Azure users. The free experience includes CSPM features such as secure score, detection of security misconfigurations in your Azure machines, asset inventory, and more. Use these CSPM features to strengthen your hybrid cloud posture and track compliance with the built-in policies.
- Cloud workload protection (CWP)– Security Center’s integrated cloud workload protection platform (CWPP), Azure Defender, brings advanced, intelligent, protection of your Azure and hybrid resources and workloads. Enabling Azure Defender brings a range of additional security features to protect you overall cloud and physical assets. In addition to the built-in policies, when you’ve enabled any Azure Defender plan, you can add custom policies and initiatives. You can add regulatory standards – such as NIST and Azure CIS – as well as the Azure Security Benchmark for a truly customized view of your compliance.
What is Azure Security Center?
Azure Security Center is a unified infrastructure security management system that strengthens the security posture of your data centers and provides advanced threat protection across your hybrid workloads in the cloud – whether they’re in Azure or not – as well as on premises.
Keeping your resources safe is a joint effort between your cloud provider, Azure, and you, the customer. You have to make sure your workloads are secure as you move to the cloud, and at the same time, when you move to IaaS (infrastructure as a service) there is more customer responsibility than there was in PaaS (platform as a service), and SaaS (software as a service). Azure Security Center provides you the tools needed to harden your network, secure your services and make sure you’re on top of your security posture.
Azure Security Center addresses the three most urgent security challenges:
- Rapidly changing workloads– It’s both a strength and a challenge of the cloud. On the one hand, end users are empowered to do more. On the other, how do you make sure that the ever-changing services people are using and creating are up to your security standards and follow security best practices?
- Increasingly sophisticated attacks– Wherever you run your workloads, the attacks keep getting more sophisticated. You have to secure your public cloud workloads, which are, in effect, an Internet facing workload that can leave you even more vulnerable if you don’t follow security best practices.
- Security skills are in short supply– The number of security alerts and alerting systems far outnumbers the number of administrators with the necessary background and experience to make sure your environments are protected. Staying up-to-date with the latest attacks is a constant challenge, making it impossible to stay in place while the world of security is an ever-changing front.
What is Azure Defender?
Azure Defender for servers adds threat detection and advanced defenses for your Windows and Linux machines.
For Windows, Azure Defender integrates with Azure services to monitor and protect your Windows-based machines. Security Center presents the alerts and remediation suggestions from all of these services in an easy-to-use format.
For Linux, Azure Defender collects audit records from Linux machines by using Auditd, one of the most common Linux auditing frameworks.
What Resource Types can Azure Defender Secure?
Azure Defender provides security alerts and advanced threat protection for virtual machines, SQL databases, containers, web applications, your network, and more.
Hybrid Cloud Protection – Utilizing Azure Arc
As well as defending your Azure environment, you can add Azure Defender capabilities to your hybrid cloud environment:
Protect your non-Azure servers
Protect your virtual machines in other clouds (such as AWS and GCP)
You’ll get customized threat intelligence and prioritized alerts according to your specific environment so that you can focus on what matters the most.
To extend protection to virtual machines and SQL databases that are in other clouds or on-premises, deploy Azure Arc and enable Azure Defender. Azure Arc for servers is a free service, but services that are used on Arc enabled servers, for example Azure Defender, will be charged as per the pricing for that service. Learn more in Add non-Azure machines with Azure Arc.
What is Azure Arc?
Azure Arc-enabled servers enable you to manage your Windows and Linux physical servers and virtual machines hosted outside of Azure, on your corporate network, or other cloud provider. This management experience is designed to be consistent with how you manage native Azure virtual machines. When a hybrid machine is connected to Azure, it becomes a connected machine and is treated as a resource in Azure. Each connected machine has a Resource ID enabling the machine to be included in a resource group. Now you can benefit from standard Azure constructs, such as Azure Policy and applying tags. Service providers managing a customer’s on-premises infrastructure can manage their hybrid machines, just like they do today with native Azure resources, across multiple customer environments using Azure Lighthouse.
How Does it Work?
To deliver this experience with your hybrid machines, you need to install the Azure Connected Machine agent on each machine. This agent does not deliver any other functionality, and it doesn’t replace the Azure Log Analytics agent. The Log Analytics agent for Windows and Linux is required when:
- You want to proactively monitor the OS and workloads running on the machine,
- Manage it using Automation runbooks or solutions like Update Management, or
- Use other Azure services like Azure Security Center.
Azure Pricing Overview
Security Center is offered in two modes:
- Azure Defender OFF(Free) – Security Center without Azure Defender is enabled for free on all your Azure subscriptions when you visit the Azure Security Center dashboard in the Azure portal for the first time, or if enabled programmatically via API. Using this free mode provides security policy, continuous security assessment, and actionable security recommendations to help you protect your Azure resources.
- Azure Defender ON– Enabling Azure Defender extends the capabilities of the free mode to workloads running in private and other public clouds, providing unified security management and threat protection across your hybrid cloud workloads. Some of the major features of Azure Defender:
- Microsoft Defender for Endpoint– Azure Defender for servers includes Microsoft Defender for Endpoint for comprehensive endpoint detection and response (EDR). Learn more about the benefits of using Microsoft Defender for Endpoint together with Azure Defender in Use Security Center’s integrated EDR solution.
- Vulnerability scanning for virtual machines and container registries– Easily deploy a scanner to all of your virtual machines that provides the industry’s most advanced solution for vulnerability management. View, investigate, and remediate the findings directly within Security Center.
- Hybrid security– Get a unified view of security across all of your on-premises and cloud workloads. Apply security policies and continuously assess the security of your hybrid cloud workloads to ensure compliance with security standards. Collect, search, and analyze security data from multiple sources, including firewalls and other partner solutions.
- Threat protection alerts– Advanced behavioral analytics and the Microsoft Intelligent Security Graph provide an edge over evolving cyber-attacks. Built-in behavioral analytics and machine learning can identify attacks and zero-day exploits. Monitor networks, machines, and cloud services for incoming attacks and post-breach activity. Streamline investigation with interactive tools and contextual threat intelligence.
Conclusion
As threats and your internal supply chain of data and infrastructure continues to expand; Microsoft is continuing to enhance and broaden their security and governance tool sets to help organizations protect and ease the IT staff burden to manage their growing internal data supply chain. Planet is in a great position to help you understand the new features and capabilities and build a roadmap to take best take advantage of these capabilities. Azure Security Center + Defender + Arc provides you with the means to reduce the management of doing, provide tools, provide visibility and your own IT operations 360 degree dashboard.
Broaden protection, increase visibility, focus on mitigation opportunities and IT disruption events will always occur but be the first to be informed vs last to know.

