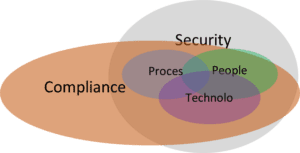
Figure 1 A visualization of security and compliance concepts
In today’s rapidly evolving threat landscape, ensuring the security of your organization’s data is paramount, and compliance frameworks can play a critical role in proving that security to the stakeholders who matter most. Let us define ‘compliance’ as the ability to prove security to stakeholders that matter in a meaningful and repeatable manner and ‘security’ as the set of actions and activities by your organization’s people, processes, and technology to achieve your organization’s definition of success for maintaining confidentiality, integrity, and availability of protected and/or valuable data.
I stressed ‘protected and/or valuable data’ because if there is no requirement to protect data (e.g., a regulatory or legal obligation) then security of that data—and devices accessing the data—may be moot. The implicit task of identifying data and information of value is woven throughout Planet Technologies’ various Enterprise Cloud Readiness (ECR) offerings, Security Assessments, and Compliance Assessments. It is also a key component of Zero Trust Architecture—know your important data.
‘Proving security’ (aka ‘compliance’) is not an assurance that an organization will be immune from a breach of integrity, confidentiality, or loss of availability of protected and/or valuable information.
Compliance instead is a repeatable process that reduces the probability of a breach—using the very same people, processes, and technologies that establish security. Additionally, compliance helps organizations systematize their actions in the event of a breach / incident, speed their recovery from a breach / incident, and generally decreases the impact to the data subjects (e.g., PII breaches) or the data owners (e.g., proprietary data).
There will be times when exigent circumstances require the appropriate organizational leaders to make decisions and accept risks. This article in no way diminishes that reality. In such situations, the organization must make choices and adapt. Ideally their choices are rehearsed and/or avoid maladaptive outcomes—which would reflect well on their incident, contingency or disaster response preparedness.
There is deliberate scoping associated with ‘proving security’ to ‘stakeholders that matter.’
Though the limitation may seem obvious, not all stakeholders are equal, and some may not be stakeholders at all. Some who should be stakeholders do not think of themselves as such. Others inappropriately ignore those with valid concerns. Of note, if an organization does not have variability in their stakeholder population, they run the risk of creating an echo chamber amongst themselves even when periodic external assessments are mandated by law or regulation.
The central thesis that Planet Technologies and I explored here, and will continue to apply in future articles, is that compliance is the ability to prove security of protected and/or valuable data to stakeholders that matter in a meaningful and repeatable manner. This conceptualization can help reduce the interminable tension between the practitioners of ‘operations,’ ‘security,’ and ‘compliance.’ It can also help leaders recognize that ‘compliance’ is not a straitjacket and that ‘security’ is not self-enforcing.
Author’s Note: In preparing for the next article in this series, a mutually agreed definition of what constitutes ‘proof’ is meaningful. For the remainder of this series, I will be generalizing to formal risk management standards/frameworks (e.g., the Cybersecurity Maturity Model Certification (CMMC), HIPAA, SOC 2, ISO 27001, and NIST 800-37 generally executed with NIST 800-53). As to whether the framework(s) chosen by a company (or inflicted upon the company) are meaningful, that depends entirely on the organization. The CMMC/NIST 800-171 framework offers a score at that end of an assessment that allows organizational leaders to assess impacts of security on their ability to get future US Department of Defense (DoD) contracts—eventually it may impact keeping existing contracts. The SOC 2 and ISO 27001 frameworks offer options for meaning and repeatability for those organizations that do not intersect with US DoD and its requirements. HIPAA’s Security and Privacy Rules provide insight to security practices of Covered Entities and their Business Associates—potentially reducing costs for insurance, reducing the probability of negligent breaches of protected data, and providing some level of protection in litigious times.

